Outsourced customer service that drives loyalty
A one-stop solution for finding and managing exceptional support talents. Improve every customer interaction while cutting operational expenses.
.avif)
Winning service outsourcing outcomes
At EverHelp, we specialize in providing comprehensive customer service outsourcing solutions tailored to your unique needs.
Of tickets solved monthly
First response rate
Average customer satisfaction rate
We work with any support channel you prefer
From dial-ins to DMs, we respond to your customers wherever they are
Inbound & outbound calling
Deliver exceptional care in every call center interaction with our outsourced customer service team. From answering customer questions to engaging prospects and clients, we’re here to ensure a positive experience.
Social media support
Get your social media channels covered, with our agents responding to customer inquiries, complaints, and brand mentions, ensuring timely responses that elicit customer care and enhance customer satisfaction.
Chat support
Deliver instant, efficient customer service with our 24/7 chat support. Our outsourcing team responds in real-time, so customers get quick, accurate answers to their questions while we keep things professional.
Email support
Use tailored outsource customer email support so each response is personalized and fast. With an average email response time of under 10 min, we deliver right customer service solutions for support cases.

Security is our priority
When outsourcing help to us, you can rest assured that customer data and all service systems are consistently protected, adhering to industry-leading practices and protocols for customer service companies.
PCI DSS Compliance
As a PCI DSS Level 1 third-party service provider, we follow the highest security protocols to protect payment data and reduce the risk of fraud during the business process. We are dedicated to maintaining secure systems that protect sensitive financial information during all business process outsourcing.
GDPR Compliance
Your privacy and data protection are central to our operations as your outsourcing partner. We are fully GDPR-compliant, ensuring that personal data is handled with the highest level of security and care, in line with international regulations for outsourcing companies.
How clients awesomize with EverHelp
Executing experience beyond expectations
Offer
Sourcing
Integration
Training
Launch
Growth
Various service integrations available
We can integrate with all major CRM systems or add a new integration just for you.
All your customer support needs, covered
At EverHelp, we help you with tailoring outsource customer service solutions that match your exact external support needs and lead to increased customer satisfaction and retention.
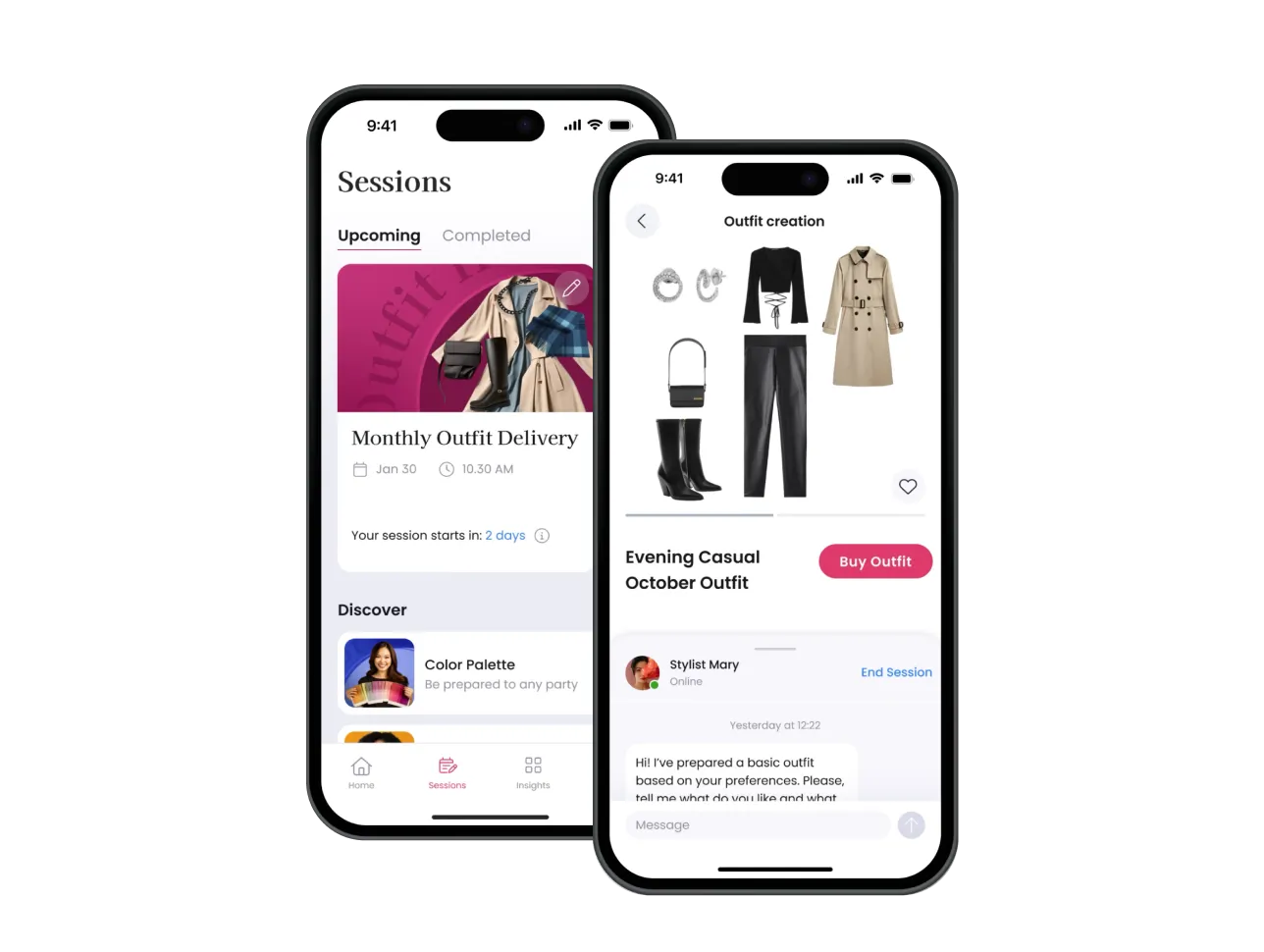
Sales service
We manage your sales pipeline. With our outsource customer service experts, you can scale your sales efforts, nurture client relationships and positive customer experience, and achieve your sales targets and customer retention goals.
Startup customer support
Grow with A+ startup support using a product-centric approach. Our help with refund and chargeback practices reduces customer churn and ensures sustainable growth and an exceptional customer journey.
Technical support service
Our top outsource customer service agents work for you, helping you manage customer support system and resolving even the toughest tickets 24/7. Expert training, product knowledge management, and QA are provided to ensure all customer requests are handled with care to provide a consistent customer experience.
Back-office support
Consider outsourcing to focus on core business activities and reduce in-house costs. Our internal support team experts manage all tedious administrative duties and cover various support functions to enhance your customer experiences.
Support that truly cares

From our blog
FAQ
Get answers to your most frequent questions
Customer service outsourcing is the practice of hiring a third-party company to handle customer support tasks for a business. These tasks can include answering customer inquiries across different communication channels, providing technical support, processing orders, handling returns and cancellations, analyzing customer experience trends, and more.
The types of outsourcing depend on location and the service provided. There are three main types of traditional customer service outsourcing based on location:
- onshore outsourcing, which is done within the same country as the business.
- nearshore outsourcing, done in a neighboring country with lower business costs.
- offshore outsourcing – a service that’s done in a distant country, often to significantly reduce labor costs.
Foremost, it’s a good way to reduce your in-house customer service costs and work with specialized experts. Additionally, it will allow you to provide 24/7 omnichannel customer assistance to handle all incoming customer requests. As such, through outsourcing support services, you can focus on core business activities, maintain quality assistance for your clients, ensure customer satisfaction and a positive brand experience, and generally grow faster, further expanding the customer base. If you are interested in learning more about this support model, we recommend reading our article on the pros and cons of outsourcing.
The cost of outsourcing customer service varies depending on factors like location, service complexity, support work hours, and the team size needed. Prices may also depend on the level of expertise required, language support, and additional features like 24/7 availability or technical support. Usually, reputable customer support outsourcing companies provide diverse pricing options. For example, at EverHelp, we have three options: dedicated, shared, and talent-only teams to match the unique support requirements of our clients. You can check out more detailed descriptions of our support models on our pricing page.
Start with pinpointing your needs: the type of support, hours of operation, channels, languages, and any additional services necessary to satisfy your customer service needs. Look for providers with a strong reputation, relevant experience, and high-quality service that aligns with your industry. Evaluate their pricing and ensure they use modern tools like AI, chatbots, and automation. Also, confirm they follow security protocols and comply with data protection regulations. Finally, ensure they offer flexibility and scalability for future growth. You can also check out a more extensive outsourcing support partner checklist on our website. Yet, if you are tired of searching, just head straight to our top list of 6 best customer service outsourcing companies.
For starters, our team helps reduce operational costs while still providing relevant, personalized, and quick assistance (under 45 seconds for first replies). As we offer multilingual support in over 30 languages, our team helps businesses to easily scale globally. With EverHelp’s all-inclusive approach, covering inbound, outbound, chat, and email support, you can also ensure timely and efficient customer care. At EverHelp we also prioritize security, being compliant with GDPR and PCI DSS to safeguard customer data. Overall, you can be sure that our outsourced agents are trained to handle queries of any complexity, guaranteeing consistent, high-quality support. If you are interested in learning more, book a call with us!













.png)















.webp)